Two Lenses on x402: A Builder and a Data Guy Compare Notes
Two builders, two telescopes on the x402 network. Phibo on the operator side, Tom on the observatory side. Here's what each saw, and what aligned.
TL;DR
- x402 is two protocols depending on where you stand: one you ship on, one you measure.
- The spec tells builders what's possible. The telemetry tells them what's actually happening — and the gap is wider than most assume.
- Of 22,056 endpoints indexed, 246 settle weekly. 47.4% of raw transactions look like wash by four public rules. Facilitator-vs-P2P split is more fragmented than first-pass tracking suggests: within the 14.5% of clean rows classified so far, 32.2% facilitator-mediated / 67.8% direct P2P. The remaining 85.5% is mid-backfill via Base RPC.
- If you're building on x402 right now, the honest questions aren't "which SDK" — they're "which 1% of endpoints are real, and who's actually paying who."
I shipped my first x402 endpoint and watched it sit there. Not broken — just quiet. The spec said "agents will discover and pay." The logs said nothing was discovering and nothing was paying. So I went looking for the agents. Turns out somebody else was already counting them.
Tom's been scanning the catalog since April 10 and indexing Base settlement since April 12. Twenty days of endpoints, eighteen days of payments. Small windows, but honest ones — and already enough to see that most of what the x402 spec implies about an agent economy is not yet what x402 does in practice. 22,056 endpoints indexed. 246 settling weekly. That's a 1.12% active ratio. 98.88% of the surface area is dormant.
So we decided to write this together. One of us builds on x402. The other measures x402. We kept comparing notes in DMs and realized the notes disagreed in ways worth publishing. This piece is the disagreement, interleaved. Phibo writes what he sees from the IDE. I write what I see from the indexer. We don't resolve every tension — some of them are the point.

Section 1 — Architecture: what the spec promises vs what endpoints need.
Phibo: The x402 spec reads clean. HTTP 402, a WWW-Authenticate header, an L402 token, a wallet that signs and pays. You can implement the happy path in an afternoon. That simplicity is real — and it's also where the first trap is.
The architectural decision that actually matters isn't which chain you pick or which SDK you wrap. It's where you put the payment gate in your agent's execution flow. Most people bolt it onto the front door: authenticate, pay, then call. That works fine for simple single-agent queries. The moment you're running orchestrated agents — a scheduler calling a grading agent calling a reporting agent — you've got nested payment flows with no shared context. Each hop needs its own wallet, its own token, its own retry logic. The spec is silent on this. You figure it out at 2am.
Retry semantics deserve their own discussion. x402 doesn't define what happens when an endpoint accepts your token but returns garbage, or times out after you've already settled. The payment cleared. The value didn't. You're now building refund logic on top of an atomic payment layer that was supposed to make refunds unnecessary. I ended up implementing an optimistic execution pattern with result confirmation before the agent proceeds. Not in the spec. Just what works.
What I wish the spec defined: a standard response envelope that distinguishes between "endpoint got your payment and processed it," "endpoint got your payment and will process it eventually," and "endpoint got your payment and something went wrong server-side." Right now those three states return nearly identical HTTP bodies and you're inferring from latency. For agents chaining ten calls in sequence, one ambiguous response poisons the whole run.
Tom: From the indexer side, I can tell you which architectural choices correlate with endpoints that settle vs endpoints that don't. Of 22,056 endpoints indexed, 15,000 are Base-resolvable (~68% of catalog) and 229 are Solana-native. But only 246 settle weekly across the whole catalog. The architecture decisions that look clever on paper (exotic chains, bespoke facilitators) map almost 1:1 onto the 98.88% dormant bucket. The endpoints that actually move USDC are boring — almost all on Base, almost all in the micro-USDC range ($0.0005–$5.00). What's more interesting is how they settle, and the answer turned out to be less clean than my first pass said. Worth a separate section (see §4). The spec gives you options. The data says the options that actually work are a narrow subset.
Section 2 — What breaks first when you ship
Phibo: Discovery is the thing that breaks first, and it breaks silently. You ship an endpoint. You set up the payment wall. You test the auth flow, it works, you deploy. Then you watch the logs and nothing happens. No agents. No payment attempts. No 402s. Just quiet. That's not a bug in your implementation — that's the discovery layer being missing. The spec assumes agents will find your endpoint. It doesn't say how.
The second thing to break is wallet UX for agents. Human wallets assume a human is watching. Agents aren't. When a transaction needs gas that isn't there, a human wallet throws a modal. An agent just... stalls. Or fails with a non-descriptive error that looks like a network timeout. I spent two hours debugging what I thought was a facilitator issue. It was a gas balance problem the agent had no way to surface. Building agent-native wallet tooling means monitoring balances proactively, setting minimum thresholds, and handling refill flows as first-class infrastructure — none of which is in any x402 tutorial.
Facilitator handoff was the 2am problem I didn't see coming. The spec describes facilitators as a routing layer. In practice, facilitator reliability is the most underexplored variable in the whole stack. When a facilitator goes down, your agent's payment attempt doesn't bounce — it hangs. No timeout specified in the spec. No fallback behavior defined. I now run a dead man's switch on every facilitated call: if no receipt within N seconds, abort the hop and flag for retry. That logic lives in my agent, not in any library.
The honest summary: most of what breaks in x402 isn't the payment primitive itself. It's everything the spec assumes is already solved — discovery, wallet ops, and facilitator health monitoring.
Tom: What breaks first for a builder maps to what I don't see in the data. I don't see autonomous discovery working at scale — I see ~401K unique payer wallets raw, ~373K after wash filtering, and I see them hitting a small, repeated set of endpoints. The long tail of 22,056 endpoints isn't being discovered by agents; it's being ignored. So when a builder ships and nothing happens, that's not a bug in their endpoint — it's the discovery layer not being real yet. The thing that "breaks first" is often the thing the spec assumes works.
Section 3 — Discovery vs trust: builder assumptions vs telemetry
Phibo: When you ship an x402 endpoint, you make implicit trust assumptions before you write a single line of payment logic. The most dangerous one: that whoever is calling your endpoint is actually an agent, executing a task, with a real use case on the other side.
The spec lets you get away with verifying almost nothing. You get a payment token. You verify the payment cleared on-chain. That's it. You have no idea who funded the calling wallet, why they're calling, whether they'll call again, or whether the "agent" is a human pretending to be automated or a bot pretending to have intent. The protocol treats all of this as out of scope.
As a builder, I defaulted to trusting by design — x402's whole premise is that payment is the trust signal. If someone paid, they have skin in the game. In theory, that's cleaner than API keys and auth tokens. In practice, it breaks down when the payment and the payer come from the same source, which is easier to arrange than you'd think.
What I actually verify: I check that the token hasn't been replayed (timestamp window + token hash cache), that the amount matches the resource tier I'm serving, and that the wallet hasn't been flagged in my own abuse table. None of that is in the spec. I built it because without it, my endpoint was callable by anyone willing to pay a cent per request — including scrapers, test scripts, and wallets I was inadvertently funding myself during development.
The trust problem in x402 isn't about cryptography. The payment proofs are solid. The trust problem is about intent — and the spec doesn't even try to solve that. It probably shouldn't. But builders need to know they're inheriting it.
Tom: Here's where it gets uncomfortable. Of 6,412,310 transactions indexed on Base over 18 days, my V1 wash filter flags 47.4% (3,038,572 transactions) as non-organic — within rounding of Artemis's proprietary 47% estimate, which I take as rough cross-validation. The rule breakdown — R1 circular, R2 rapid-repeat, R3 co-funded, R4 burst — is published with methodology at smartflowproai.substack.com/p/how-i-filter-wash-trading-on-x402. The most productive single rule is R2 rapid-repeat — same payer/recipient pair settling 3+ payments inside a 60-second window:
SELECT from_wallet, to_wallet, COUNT(*) AS repeats
FROM payments
WHERE wash_flag IS NULL
GROUP BY from_wallet, to_wallet,
strftime('%Y-%m-%d %H:%M', timestamp)
HAVING repeats >= 3;Six lines, runs in seconds against the full table, catches roughly a quarter of all wash signal on its own. Builders assume their endpoint is being called by agents. Sometimes it is. Sometimes it's being called by a wallet that was funded 90 seconds earlier by the same source that funds the "agent" calling back. Trust is a data problem before it's a protocol problem.
Tom note (counter-receipt before facilitators): I run my own x402 endpoint via Orbis since April 17. Dashboard: 57 settled micropayments across two claim cycles, $0.0944 USDC lifetime. Tiny — but sustained, on-chain, and arrived without any marketing. So "agents will discover and pay" isn't always vapor; it works on marketplace surface area at micro-USDC scale. The discovery layer just isn't general-purpose yet.
Section 4 — Facilitator strategy vs facilitator reality
Phibo: The facilitator decision looks like a routing question. It isn't. It's an infrastructure ownership question, and the answer you choose has consequences that don't show up until you're in production.
When I started building, I defaulted to Coinbase's CDP facilitator because it was the path of least resistance. It worked. Until it didn't. Not in a catastrophic way — in a subtle way. Latency spikes during high-demand windows. Occasional silent drops where a transaction was submitted but confirmation came back ambiguous. And the biggest issue: I had zero visibility into why. The facilitator is a black box. You can't ask it why your transaction took 12 seconds. You can't tell your agent to route around it.
Going pure P2P is the honest architecture. You control the whole path. Your agent submits directly to Base, waits for on-chain confirmation, and there's no intermediary to mishandle the handoff. The downside is that you now own the gas management, the RPC reliability, the confirmation polling logic, and the fallback behavior. It's more code. It's also more observable code, which I've come to value more than conciseness.
Running your own facilitator is the middle path that sounds smart until you think about the maintenance burden. You're essentially operating infrastructure for a payment network. That's a full-time job at scale, and for most product builders it's a distraction from the actual product.
My current position: P2P with a hardened agent-side transaction manager — retry windows, gas buffer monitoring, receipt caching, dead man's timeouts. It's more upfront work but it means when something goes wrong, I know exactly where to look. For the emerging markets context I build in, where every hop through a US-based facilitator adds latency and jurisdiction risk, this also just makes practical sense.
Tom: The decision looks different from the telemetry, and I owe a correction here before I say anything else. Two weeks ago I would have told you 99.82% of x402 settlement on Base is direct P2P and 0.18% is Coinbase CDP. I shipped that number. I retracted it on 22 April. The tracker that produced it reads USDC Transfer events on Base, which is fine for seeing payer→recipient — but the CDP facilitator settles via EIP-3009 transferWithAuthorization where the facilitator is tx.sender on-chain and the Transfer event looks identical to a direct P2P payment. The indexer was silently blind to facilitator routing.
Of 6,412,310 raw Base x402 transactions over 18 days (April 12 → April 30), 3,373,738 clean after wash filter. The facilitator-vs-P2P split is currently complete for 14.5% / 489,519 of the clean subset; the 85.5% balance is mid-backfill via eth_getTransactionByHash sweep against Base RPC. Within the classified subset, 67.8% settle P2P vs 32.2% facilitator-mediated — significantly higher facilitator share than the early-April n=200 sample (and orders of magnitude higher than my retracted 99.82% claim). Number-history at smartflowproai.substack.com (corrections logged inline). Settled full-coverage numbers ship in Weekly Intel #3 in May.
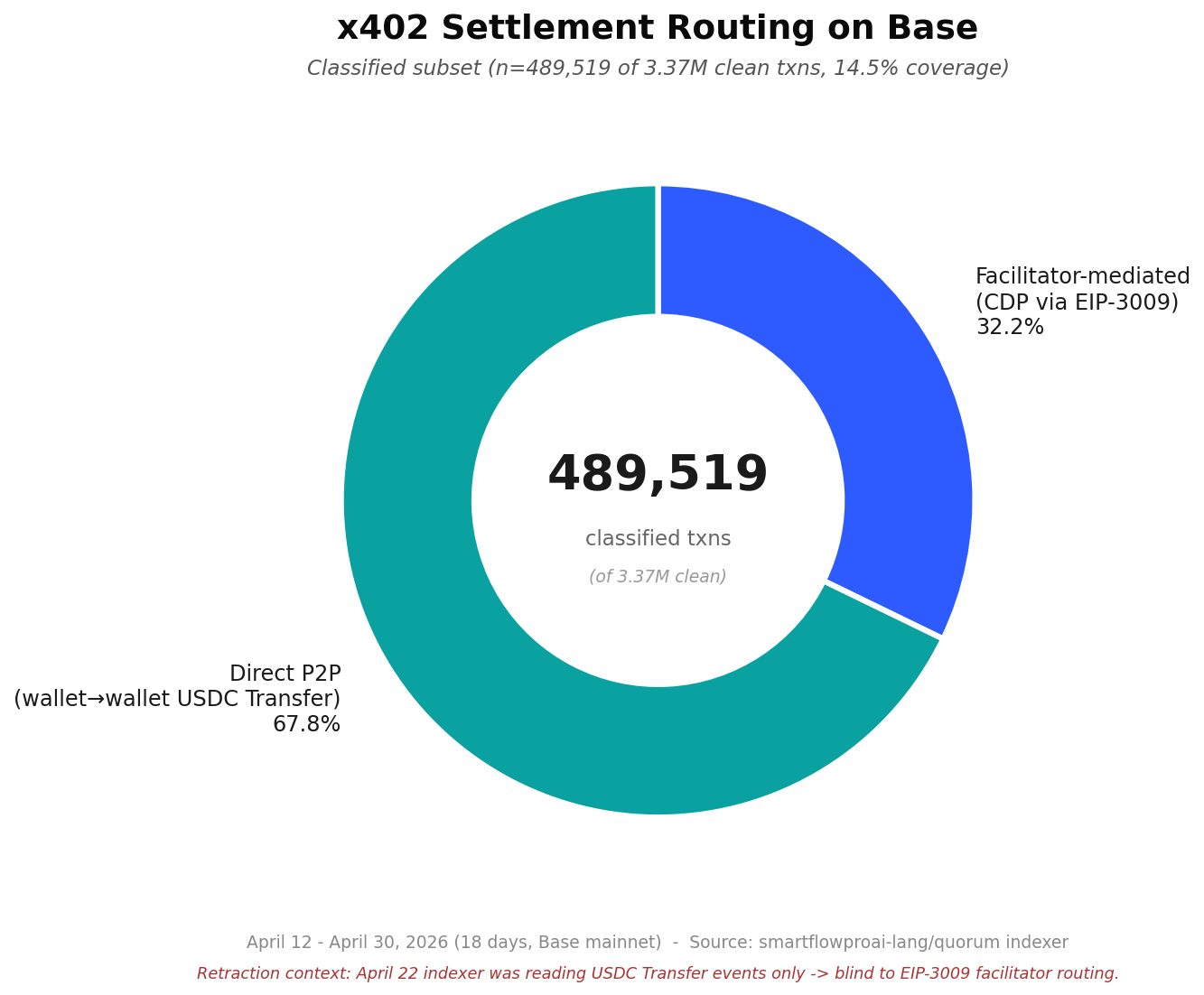
Which reshapes your section above. Running pure P2P is still a defensible architecture — direct-P2P traffic does exist at roughly 2 in 3 classified transactions. But "CDP is a rounding error" was my tracker lying to me. If you're building a facilitator play, you're competing for a meaningful share of a fragmented settlement layer, not for crumbs of a P2P-dominated one.
If you're building: ship on Base, settle P2P or facilitator-aware (don't assume one is rounding error), assume discovery is manual, and verify the other side before you trust the traffic. If you're measuring: publish your methodology and your retraction history or your numbers don't count. If you're just watching: the next 90 days decide whether x402 becomes infrastructure or stays a demo.
- Code & data: https://github.com/smartflowproai-lang/quorum
- Tom's reads: dashboard at https://smartflowproai.com/intel-k7x9m2/
- Methodology at https://smartflowproai.substack.com/p/how-i-filter-wash-trading-on-x402
- Weekly Intel series at https://smartflowproai.substack.com/